Information security is paramount at Globality.
We invest considerable resources to provide a safe, secure platform to our partners, customers, and employees. Our dedicated information security team is committed to protecting our systems through continuous research, implementation of cutting-edge technology, and subject-matter expertise. Our security policy is guided by Globality’s core values, code of conduct, and business ethics. It dictates how we operate anywhere, any time.
The Globality platform is designed, engineered, built, and tested for security every step of the way.
Our product managers, engineers, and QA testers are trained to identify information security risks and concerns as they work, from whiteboard sketches to production code deployment. Our devops engineers then ensure that our secure code runs strong and true on resilient, redundant, and highly available infrastructure.
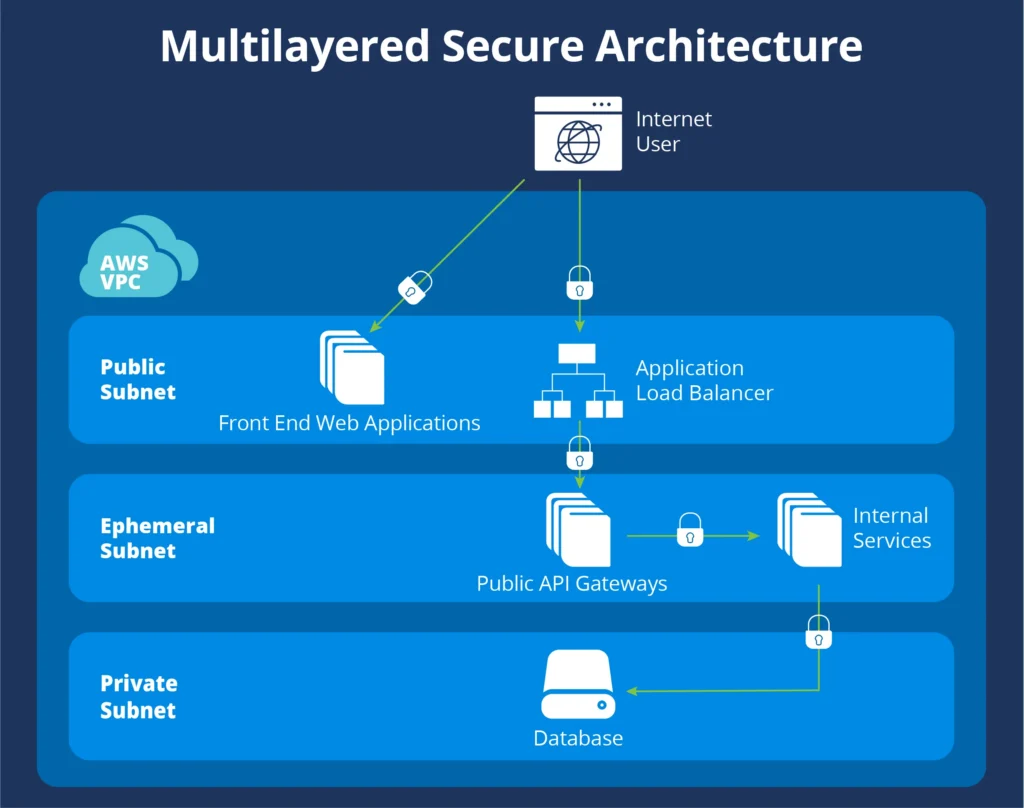
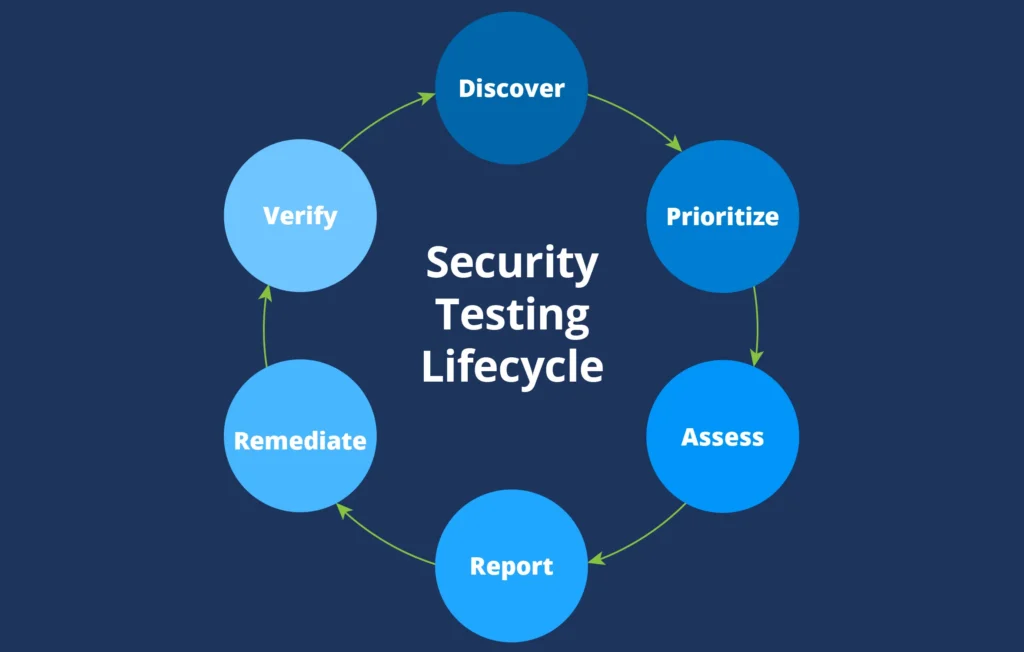
We peer-review, audit, and pen-test our products before and after they are released to production using an arsenal of manual and automated code scanners and vulnerability finders. Our tiered architecture provides multiple layers of protection, each nestled behind its own firewall. WAFs, IDS, and DLP systems complete this picture, resulting in a strong, secure, and resilient enterprise-grade offering.
Globality maintains multiple identical, separate environments for development, testing, demo, and production. Each environment operates in its own silo, where components have access only to their immediate neighbors. For example, our data layer is accessible only to the services that control and handle data, never to our web servers, application servers, or network infrastructure.
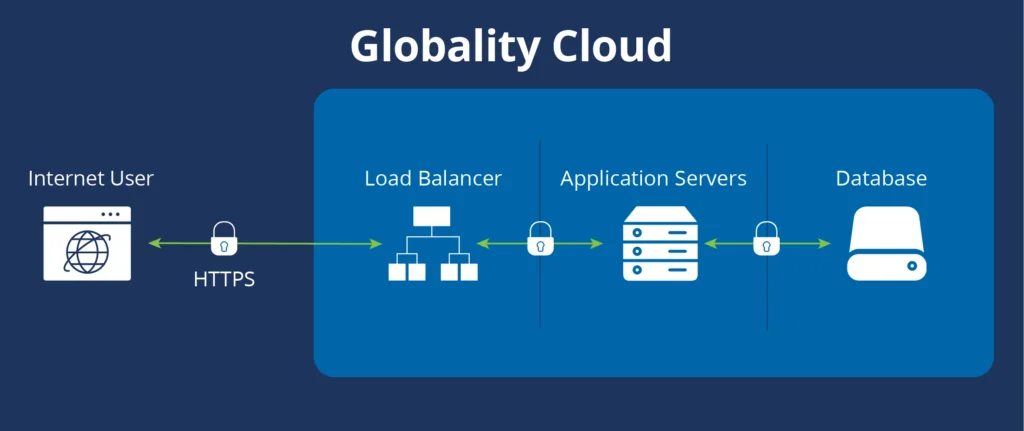
The only part of the Globality platform that is publicly accessible over the Internet is our front-end load balancers, heavily protected by layer-3 and web application firewalls. Our web servers are safely situated behind those load balancers, protected by an additional firewall layer.
Globality protects its information systems from DDoS attacks using a combination of application-level performance-adjustment mechanisms and infrastructure-embedded technologies that are developed and maintained directly by our cloud service provider. We deploy intrusion detection systems (IDS) throughout our infrastructure and on any relevant instances and components. Our IDSs are configured to alert the information security team about any irregular use at the network or application layer.
Production resources are protected by dedicated controls with access limited to select individuals who are specifically trained, authorized, and continuously monitored.
Globality uses custom, pre-built images to create all its server instances. These images have been carefully constructed and configured to eliminate unnecessary services and are routinely patched to ensure minimal security risk.
A set of automated tools construct, configure, and populate our entire stack. They are restricted via individual session keys, to be used by authorized personnel only.